Summary: CMMC 2.0 is active, enforceable, and increasingly embedded in contract eligibility decisions. Organizations that treat self‑assessment as a strategic initiative are better positioned to compete and adapt.
Introduction
As the DOD operationalizes the Cybersecurity Maturity Model Certification (CMMC) framework, defense contractors are entering a new compliance environment. CMMC 2.0 is active, enforceable, and increasingly embedded in contract eligibility decisions.
For contractors, subcontractors, and vendors that handle Federal Contract Information (FCI) or Controlled Unclassified Information (CUI), self‑assessment is now a critical business function. Inaccurate representations, incomplete documentation, or misunderstood requirements can jeopardize contract awards and create legal and financial exposure.
CMMC addresses a long‑standing weakness in the defense supply chain. Prior reliance on self‑attestation under DFARS 7012 and National Institute of Standards and Technology (NIST) Special Publication (SP) 800‑171 did not prevent recurring cyber incidents. Many organizations believed they were compliant until systems were tested or compromised.
CMMC 2.0 refines that model. It reduces complexity from earlier versions while clarifying expectations, assessment paths, and enforcement mechanisms. It also introduces real consequences for misrepresentation, reinforcing accountability across the DIB. Representations submitted through systems such as the Supplier Performance Risk System (SPRS) are treated as formal attestations. Inaccurate submissions may create exposure under statutes like the False Claims Act, elevating cybersecurity to a governance issue that requires executive oversight.
Self-assessment is an organizational responsibility
One of the most common missteps organizations make is treating the CMMC self‑assessment as a task exclusively for IT teams. While many controls are technical, compliance touches nearly every part of the organization. Policies, procedures, access management, incident response, training, vendor oversight, and documentation all require coordinated input. Leadership involvement is essential to allocate resources, define accountability, and align cybersecurity objectives with business strategy.
CMMC compliance is also continuous. Controls must be maintained, reviews conducted on defined schedules, and evidence retained over time. Leveraging GRC tools (e.g., Aprio’s CMMC Continuous Monitoring Tool) can also help teams streamline compliance processes and save valuable time.
Scoping your CUI environment with precision
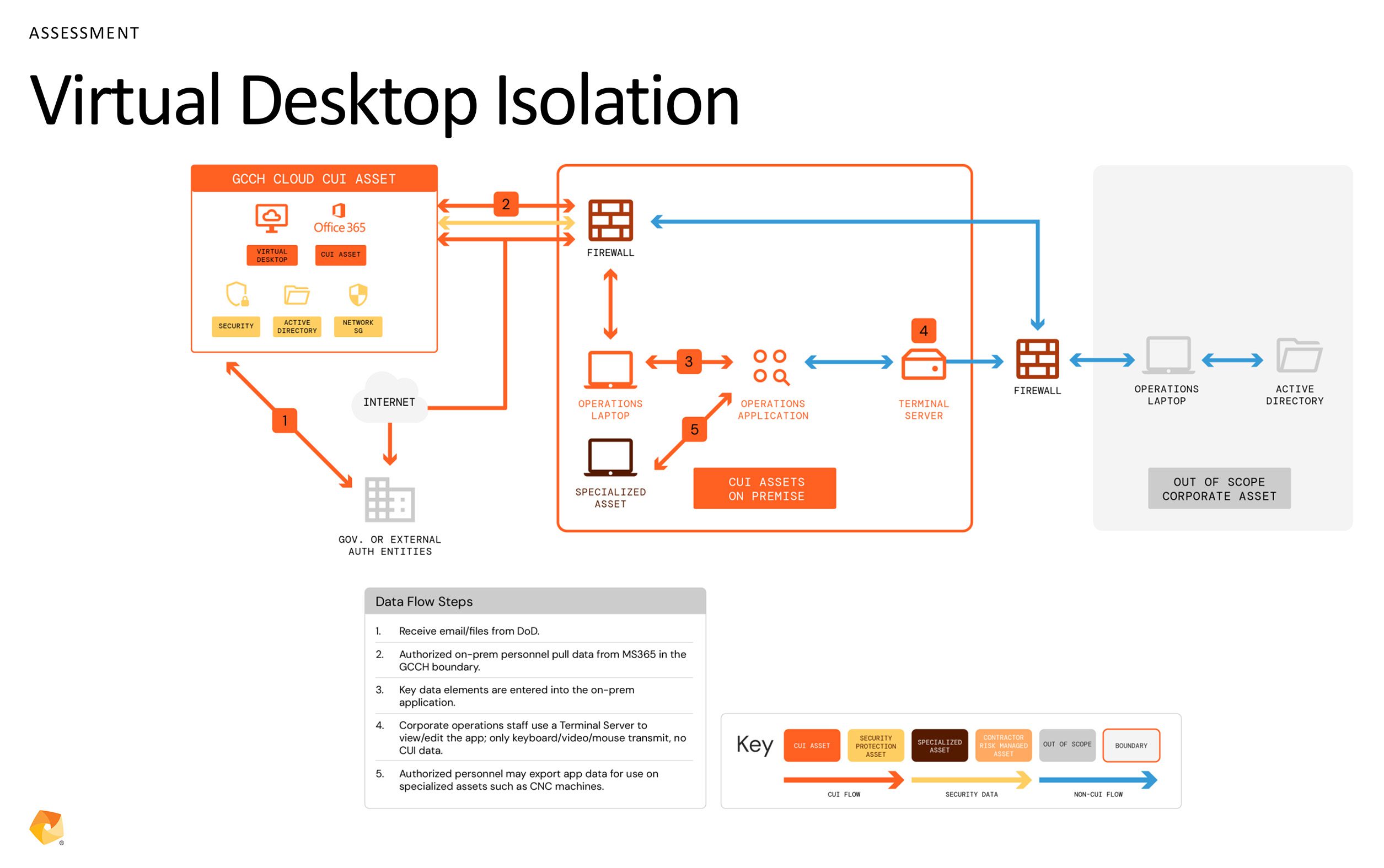
Accurate scoping is foundational to any defensible self‑assessment. Organizations must identify where CUI exists, how it flows, and which systems interact with it.
This process often reveals unexpected exposure. CUI frequently appears in email systems, shared drives, collaboration platforms, removable media, or unmanaged applications. Effective scoping combines discovery tools with cross-functional stakeholder interviews and documentation reviews.
Once CUI locations are identified, clear boundaries must be defined and documented. Network diagrams, data flow maps, and system inventories help demonstrate what is in scope and what is not.
Be careful of “overscoping” as it increases cost and complexity and “underscoping” as it creates audit risk and can undermine an otherwise strong compliance posture.
Figure 1: Data flow diagram for in-scope and out-of-scope scenarios.
Documentation as a strategic control
Documentation is not a formality in a CMMC self‑assessment; it is a primary control. The System Security Plan (SSP) serves as your foundation, explaining how each requirement is implemented within the CUI environment. A strong SSP goes beyond restating requirements. It shows how policies translate into procedures, how procedures are enforced, and how effectiveness is validated.
Supporting artifacts matter just as much. Access reviews, configuration settings, training records, incident response exercises, and audit logs all contribute to the evidence base. Documentation must remain current, accessible, and clearly mapped to specific requirements.
Common technical controls that create gaps
Certain technical requirements consistently present challenges during self‑assessment. Addressing these areas early on reduces remediation pressure and limits last‑minute surprises:
- Data loss prevention: Controls must prevent CUI from leaving controlled environments. Without monitoring and enforcement, boundaries are difficult to defend.
- Multi‑factor authentication (MFA): MFA is expected across most access points to CUI. Exceptions are limited and should not be assumed.
- FIPS‑validated encryption: Compliance requires validated products and configurations. Theoretical alignment is not sufficient.
Vendor, cloud, and supply chain considerations
Any third party that stores, processes, or transmits CUI must meet the applicable CMMC requirements.
Cloud service providers handling CUI must obtain Federal Risk and Authorization Management Program (FedRAMP) Moderate authorization or be able to demonstrate equivalent compliance. If a provider cannot meet this threshold, internal controls will not compensate.
Vendor risk management should be systematic and ongoing. Contracts, attestations, and technical validation all play a role in maintaining compliance across the supply chain.
SPRS scoring and legal accountability
Self‑assessment results are submitted to SPRS, where contracting officers verify eligibility. Each of the 110 NIST SP 800‑171 requirements contributes to the overall score, with weighted values reflecting relative risk. Some deficiencies may be addressed through Plans of Action and Milestones (POA&Ms), while others allow little to no flexibility. Inaccurate submissions create legal exposure.
Annual affirmations by senior officials reinforce the seriousness of the process. CMMC compliance represents a formal statement of organizational posture, not an internal checkpoint.
Final thoughts
While CMMC 2.0 is currently based on NIST 800-171 Revision 2, Revision 3 has already been published. While not yet the standard for CMMC, it signals where the goalposts are moving. Forward-thinking leaders are already reviewing Revision 3 to help ensure their security architecture is futureproof.
Organizations that treat self‑assessment as a strategic initiative, engaging leadership, investing in documentation, and embedding controls into daily operations, are better positioned to compete and adapt.
Did you miss our “Inside the Self-Assessment: CMMC Guidance from an Authorized CMMC C3PAO” webinar? Watch the on-demand webinar today to gain deeper insights into how to prepare and submit your CMMC self-assessment.