At a glance
- Main takeaway: It’s time for SMB owners to toss away the notion that due to their business size they are immune to cyberattacks. The reality is that they are at more risk because they lack the sophisticated security used by larger business. Today, there are affordable solutions that have been scaled to meet the needs of businesses of every size.
- Impact on your business: For any business, the cost of doing nothing is more damaging. However, for SMBs the more harmful the attack can be on your systems and if you don’t detect an attack when it happens it will be harder to respond and recover from the technical and financial impacts.
- Next steps: Aprio’s Digital Advisory Services team can perform a security health check to determine your risk level, and we can help you develop a cybersecurity framework tailored to your company’s needs.
Are you ready to learn more? Schedule a conversation with our team.
The full story:
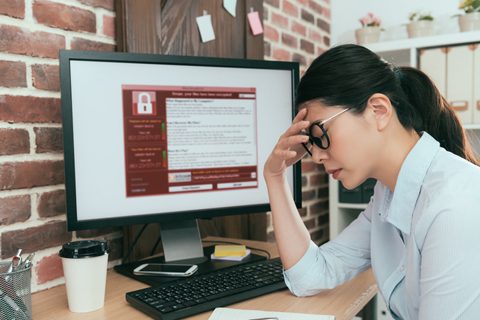
Cyberattacks are disproportionately impactful on small and medium-sized businesses (SMBs), and yet, many believe they are immune to attacks because they operate under the misguided mindset of “what could I possibly have that a hacker would want?” The answer, quite a bit.
According to the U.S. Small Business Administration, in 2020 alone, there were over 700,000 cyberattacks on SMBs with damages totaling $2.8 billion. And those numbers continue to rise steadily every year.
The National Institute of Standards and Technology (NIST) has established a cybersecurity framework that is universal to every organization no matter their size and consists of five key functions — identify, protect, detect, respond and recover. When implemented properly, these five cybersecurity functions can provide any organization with a comprehensive security approach to reduce risks. Below is a closer look at each key function:
Identify
SMBs often lack a good understanding of what systems they use and the type of information they are collecting. So, the first step in your cybersecurity framework is identifying what capabilities are essential to running your business and what data needs to be protected.
To do this, start by creating an application portfolio outlining the answers to these questions:
- What is your primary business function?
- What applications do you have and how do they support your business?
- What data needs protection and are there any requirements as to how it should be protected?
Creating an application portfolio lays the groundwork for your entire cybersecurity framework. If you cannot identify what capabilities and data drives your business, then you will not be able to effectively protect them and your business.
Protect
Once you’ve identified what you have, the next step is to determine the most effective way to protect it. SMBs who take a lenient approach to cybersecurity not only put their own systems and data at risk, but they also jeopardized their customer’s data. In a 2022 Digital.com survey of SMBs with 500 employees or less, 51% responded that they have customer data that is unsecure and could be compromised, and yet, 59% of SMB owners admitted that they do not have adequate cybersecurity measures in place.
In today’s digital environment, cybersecurity begins with access and identity control. No matter the size of your business, how your company thinks about access and identity control needs to be modified because most companies are using a Software as a Service (SaaS) application and employee workstations are connected to wireless internet wherever they chose to work, whether that be in their homes, at the coffee shop near their home, at an airport, etc.
How do you login and assign access rights to your systems, applications and data? Are you using multi-factor authentication to create unique IDs and passwords as well as another form of authenticating the person logging in really is who they say they are?
Since the uptick in remote jobs, workstations are exposed more now than ever, and you must ensure you have an Extended Endpoint Detection and Response (EDR) software in place to protect your systems, data and workstations from unauthorized access and monitor for signs of an attack. Modifying your security approach to match today’s internet-based working environment will allow you to look at where your exposures are and shift your security accordingly to those endpoint devices that protect your systems, capabilities and data.
Detect
Now that you know what you have and basic security features in place to protect your endpoint devices, you need to ask yourself — What am I doing to monitor those systems to ensure that if something bad does happen, it is detected and not overlooked?
Detection is crucial to protect your systems and the information you collect from potential attacks. You need to continuously monitor for unauthorized access, so you can take the appropriate action and quickly. This can be done in a few different ways:
- Assign a person or team in-house dedicated to monitoring your systems, or
- Hire a third-party Managed Security Service Provider (MSSP) to monitor your systems and alert you of any high-risk events.
The average length of time it takes somebody to detect that their systems have been hacked can be measured in months, especially for SMBs. The shorter period of time that a hacker has in your systems, the less harm they can do. However, if it takes months to detect an attack, then they can do significant damage that you may not be able to recover from.
Respond
Do you have a written plan of action to advise your organization on how to respond should a cyberattack occur? For example, say you are in the healthcare industry and your data is breached. There are specific and legal reporting requirements that would need to be addressed in the event of a security breach.
This part of the cybersecurity framework is truly dependent on how you completed the previous functions — identify, protect and detect. Knowing what you have, understanding how it needs to be protected and establishing a monitoring process are critical to determine the best way to respond to a cyberattack. Your company should designate an incident response team whether it be internally or via a third-party whose responsibility it is to follow the written action plan so there is adequate communication.
Why is a response plan so important? Because you’ll be able to contain and recover from the attack faster if you plan ahead of time. Speed of containment and recovery are crucial for your response to be successful.
- Speed of containment because the individual will steal less or impact fewer systems.
- Speed of recovery because your recovery determines how impactful the attack was on your business.
Recover
Do you have a mechanism in place to restore your services, data and facilities so can get them up and running within a reasonable amount of time? Recovering from a cyberattack is primarily ensuring you have adequate and effective backups in place.
So, when we talk about backups for SMBs, the most important thing is to ensure you have a backup that is isolated and separate from your primary systems, so you do not lose any data. While backups are vital to the recover function, they are only helpful if they work. Once you have your backup in place, you must then go through a testing and validation process and actually ensure your backups are operating properly and all the information that is critical to your business is there and can be accessed.
The bottom line
There is a big cost in doing nothing, especially for SMBs. The smaller the business, the more damaging and paralyzing the attack will be on your systems, and if you do not detect it when it happens it will be harder to respond and recover.
No matter what stage your business is in, Aprio’s Digital Advisory Services team can perform a security health check to determine your risk level and help you develop a cybersecurity framework tailored to your company’s needs.
Related Resources
Migrating to the Cloud: Security Should Be Your Priority, Not an Afterthought
Due Diligence Through a Cybersecurity Lens
Patch or Be Hacked
About Aprio’s Digital Advisory Services